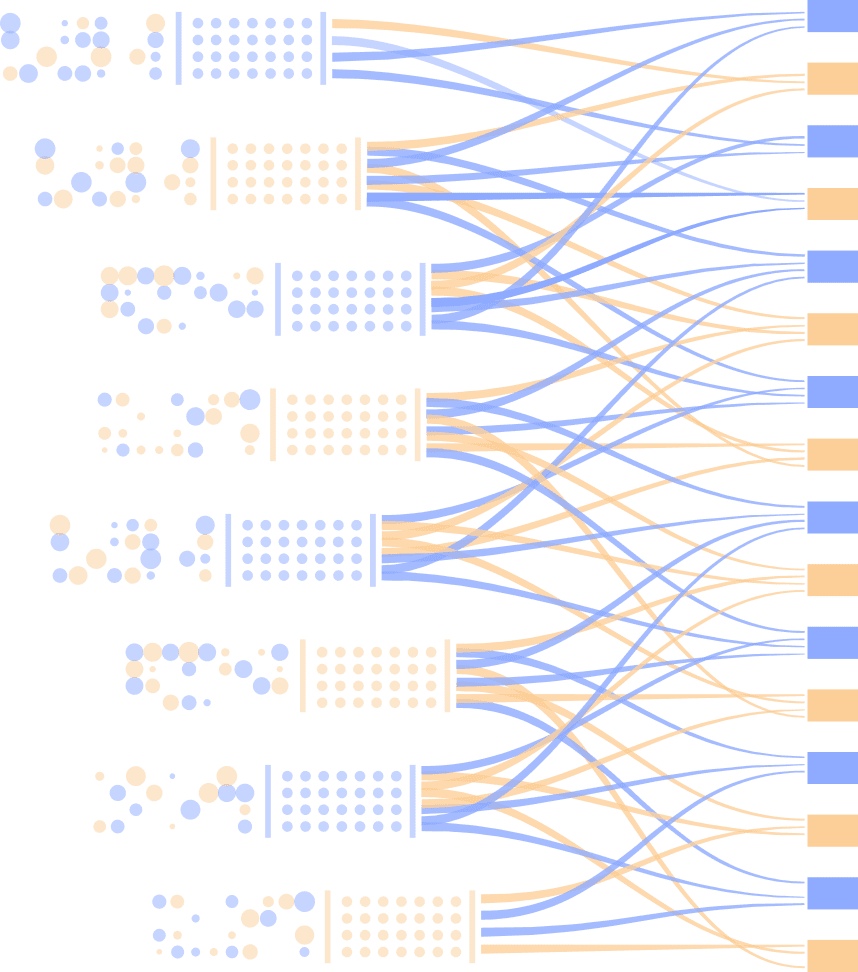
Gather Data
Apply Intelligence
Deliver Action
In our review of security cases, we have demonstrated several constant post-review abilities in our clients: a 70% Reduction in False Positives, a 4-5X Increase in use cases, 35+% Increase in overall efficiency.